Maintain Cash Flow easily with CRM software. Keep an eye at all product / service payments.
Contact Management Modules
STS CRM is the leading CRM in Egypt for Contact Management. It covers whole Marketing & Sales cycle in depth, starting from new Lead to happy customer:
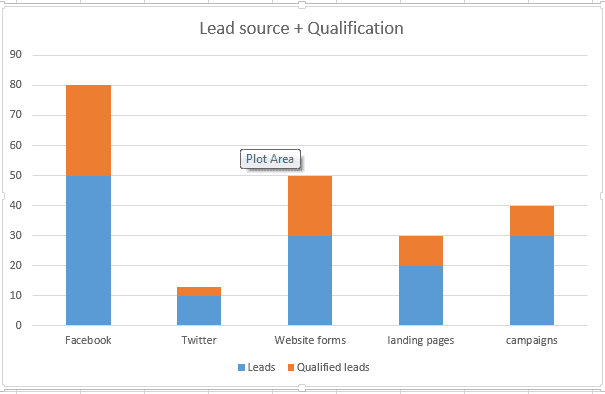
- Lead Generation & Scoring
- Account Structures
- Notification & Alerting
- Contact Profile
- Activity Log